PagerDuty Integration
Foxpass can integrate with your PagerDuty on call schedule to help automate access to sensitive resources. Just enter your API key and we'll match your Foxpass Engineering User with their corresponding ID in PagerDuty. Then, we'll continually monitor your on call schedules and add any on call users to specified groups and host groups for the duration of their on call rotation.
Additionally, you can set up a web hook in PagerDuty to notify Foxpass whenever there's an incident. We'll then automatically add any incident responders from that incident to your specified groups and host groups in Foxpass. This will ensure that any users not on call have access to your sensitive resources on an as-needed basis.
Syncing your on call schedule
In PagerDuty, go to Configuration > API Access. Then, create an API Key. It can be Read-Only.
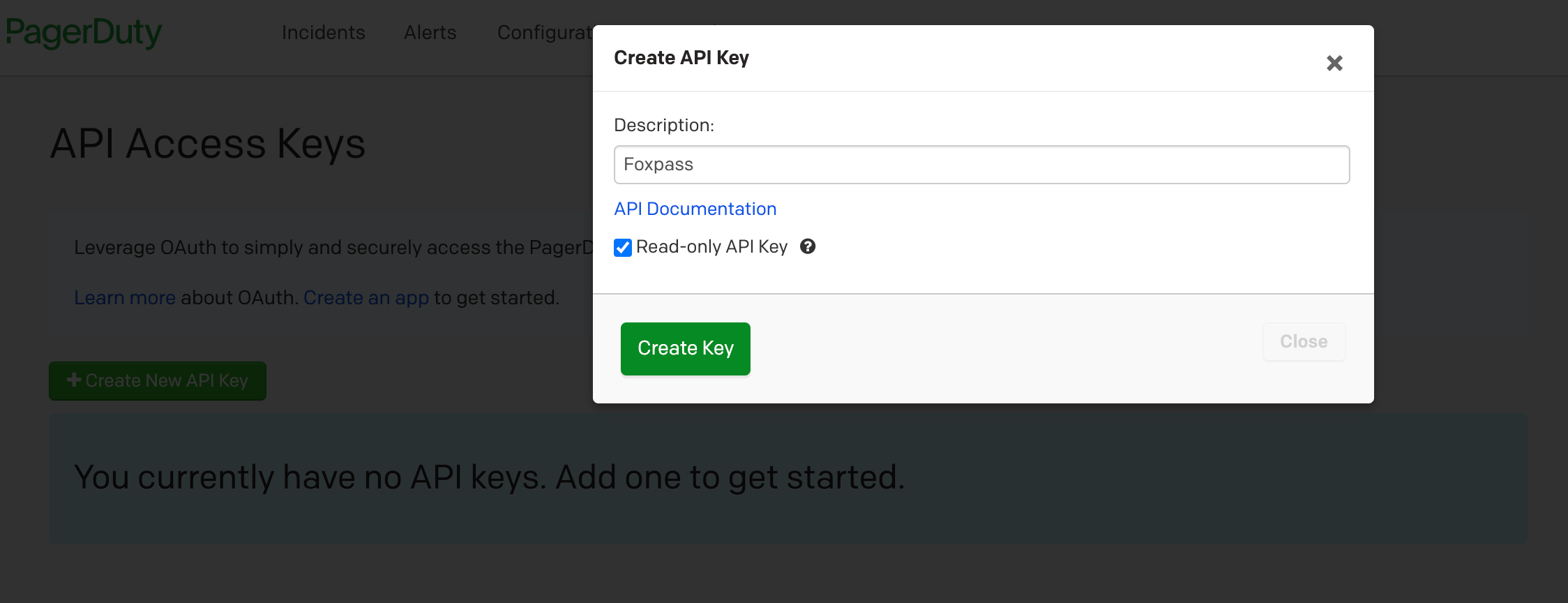
Create an API key for Foxpass
Enter that API Key into Foxpass on the PagerDuty page. This will set up an ongoing sync between PagerDuty and Foxpass that pulls in the current on call schedule. After you've entered in the key, click the Sync Now button to immediately pull in the latest rotation. You may need to wait and refresh the page to see the results after sync has run. Only Foxpass Engineering Users will be associated with PagerDuty information.
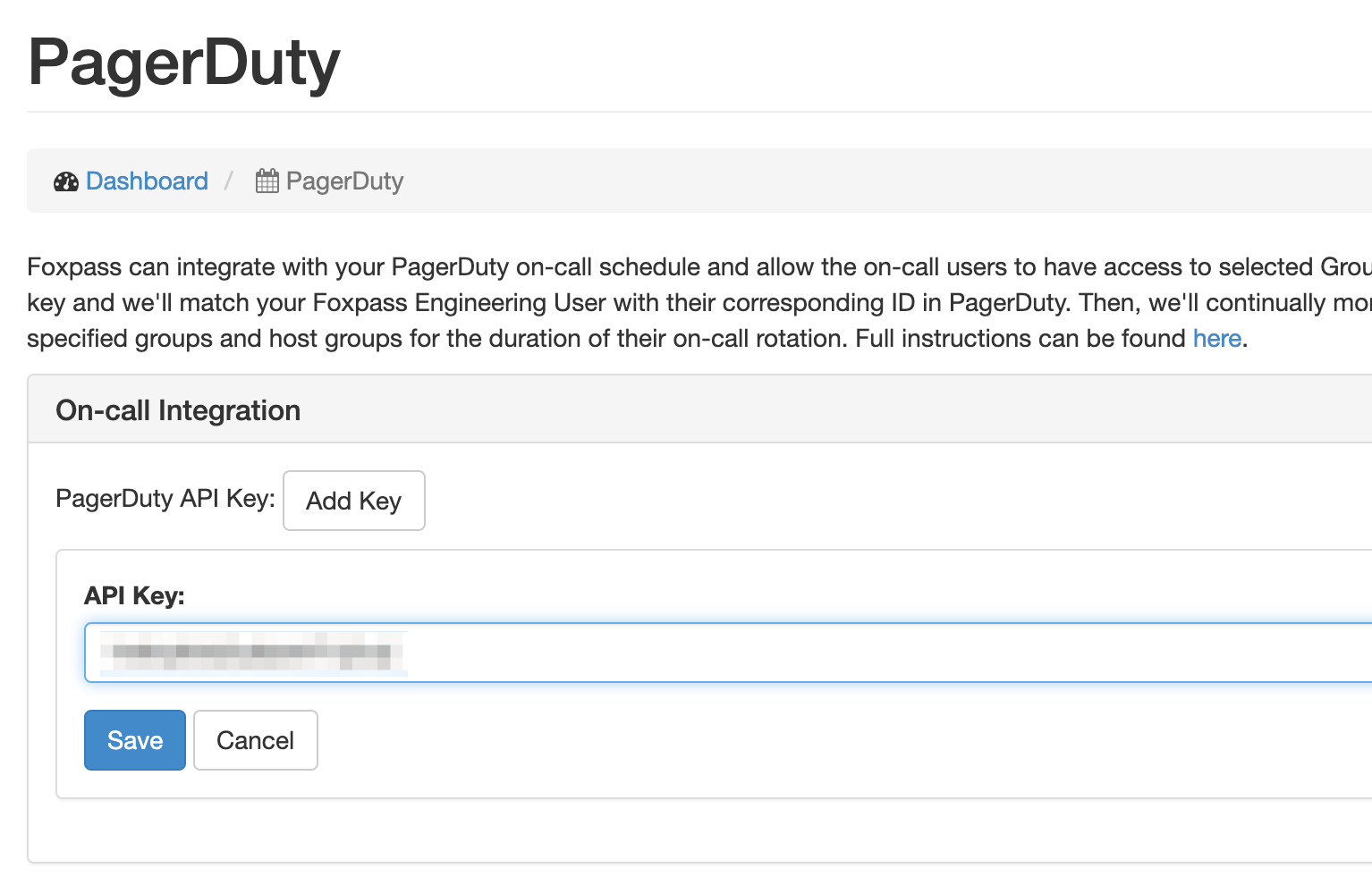
Start the sync process
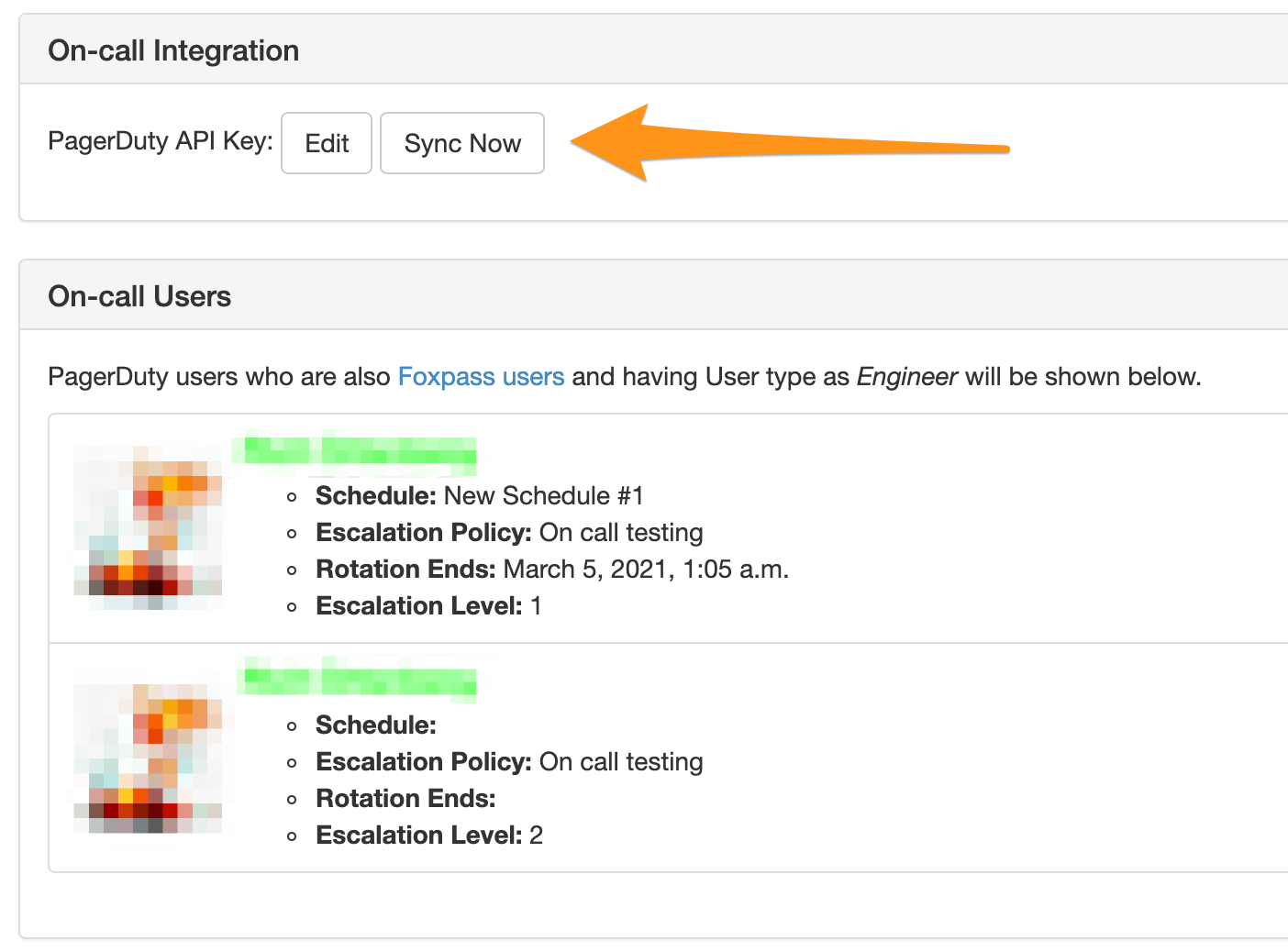
Successful sync
Configure which groups and host groups you want on call users to get access to. Once you add these groups, sync will need to run again before the users are added to the appropriate groups and host groups.
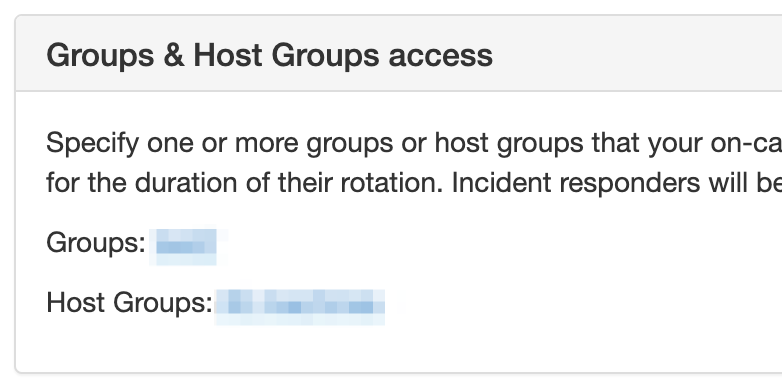
Configure your groups and host groups
Setting up a webhook
If you regularly re-assign or escalate incidents to users who are not on call, you should enable the webhooks feature. This way, all the necessary people will have access on an as-needed basis. When an incident is triggered, re-assigned, escalated, or resolved, PagerDuty will send Foxpass a notification with relevant details. If a user assigned to an incident is not in one of the specified groups or host groups in Foxpass, they will be added.
To set up the webhook integration, click the Enable Webhooks button at the bottom of the page. This will generate a single use API URL for you to enter into PagerDuty. Click the URL to copy it to your clipboard.
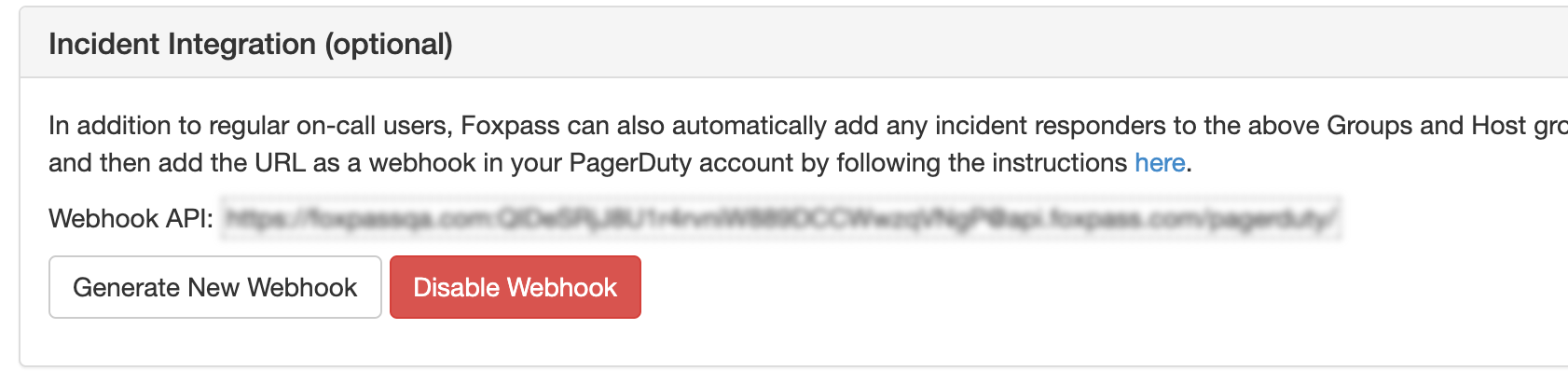
API Webhook
Next, you will need to integrate the webhook with any relevant PagerDuty Services. Navigate to the Extensions page via Configuration > Extensions. At the bottom of the page you will see an Service Extensions section. Click the New extensions link.
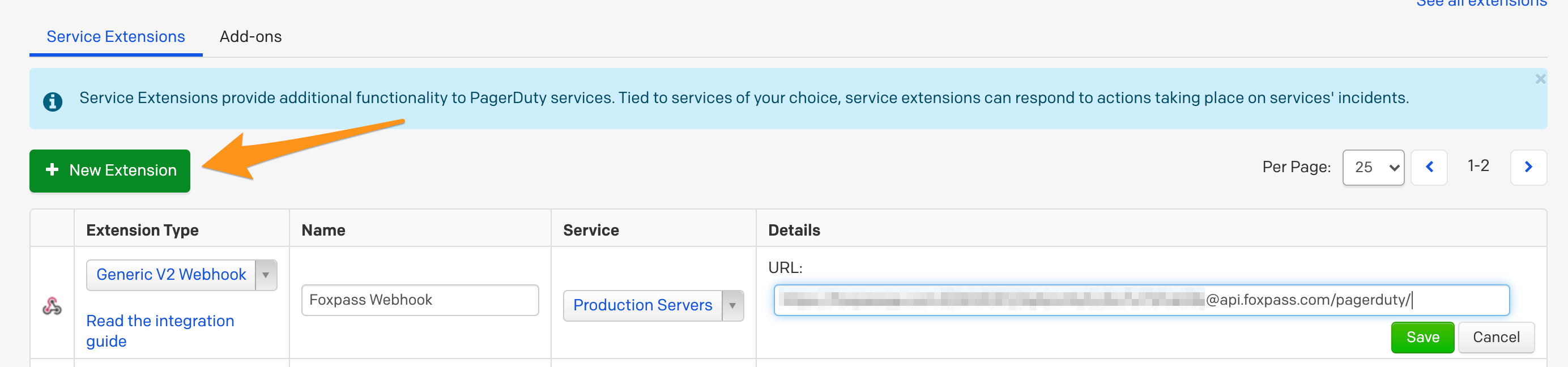
Manage extensions
Add a new extension with the following settings:
- Extension type: Generic V2 Webhook
- Name: Foxpass Webhook (or whatever you'd like)
- Service: Whichever service you want to integrate with
- URL: The url generated in Foxpass
Once an incident is triggered for that service, a notification will be sent to the Foxpass API using that URL.
A list of recent incidents with relevant information will be displayed in Foxpass, so you can double check that the integration is functioning correctly.
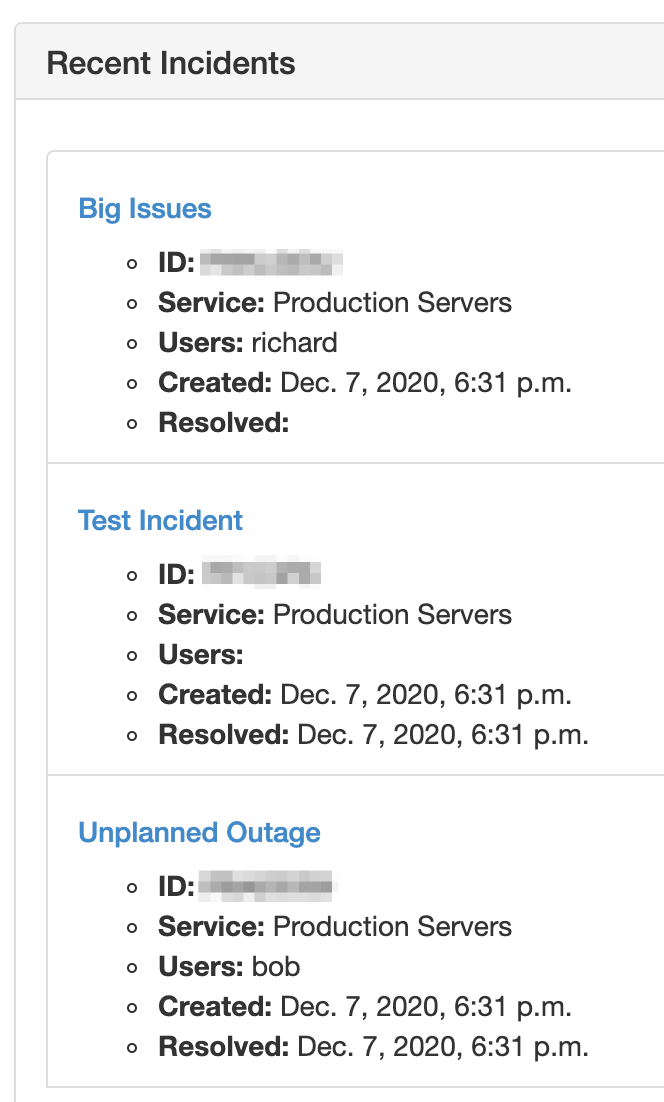
Recent incidents
Troubleshooting
The URL contains the special identifiers and security credentials for the request, but if you'd like to rotate the credentials you can click the Generate New Webhook button on the PagerDuty page in Foxpass.
If there is a misconfiguration with the webhook URL in PagerDuty, or there is a failure to properly send and process the webhook, PagerDuty may silently disable the integration. To re-enable it, first double check that you have the same URL in Foxpass and PagerDuty. Then, go back to the PagerDuty Extensions page for the service and click the Re-enable button.
Updated 7 months ago
