Google LDAP / Foxpass password delegation
Password Delegation for RADIUS is not compatible with PEAP. You must use EAP-TTLS-PAP (preferred) or PAP.
This page describes how to set up Foxpass to delegate authentication to Google's LDAP, bypassing Google's MFA.
Why Use Google Secure LDAP
Our regular Google delegated authentication cannot check passwords for accounts configured with Google's MFA. However, we can get around this restriction by using Google's LDAP endpoint to check passwords, bypassing MFA.
By using Google's LDAP as a delegated authentication source, we can expose Google's LDAP to RADIUS and non-TLS based systems by acting as a proxy.
Note: Use of Google's LDAP requires a license to one of Google Workspace Business Plus; Enterprise Standard or Plus; Education Fundamentals, Standard, Teaching and Learning Upgrade, or Plus; or Cloud Identity Premium.
Set Up Google Workspace Enterprise Plus or Cloud Identity Premium
Sign up for Google Workspace Enterprise Plus, Cloud Identity Premium, G Suite for Education, or G Suite for Education using the links below:
Google Workspace Enterprise Plus - https://support.google.com/a/answer/7284269
Cloud Identity Premium - https://cloud.google.com/identity/
G Suite Enterprise for Education - https://support.google.com/a/answer/7370133
G Suite for Education - https://edu.google.com/products/gsuite-for-education/
Google Workspace Enterprise Plus, Cloud Identity Premium, G Suite Enterprise for Education, or G Suite for Education is required for Secure LDAP use as shown by these docs.
Next, assign Enterprise or Cloud Identity licenses to your users that use Foxpass. You can read more about how to assign a license here:
https://support.google.com/a/answer/1727173
Create and Configure the Foxpass Client
Google needs to register each LDAP client that connects to it separately. You'll need to create a specific entry for Foxpass in Google. Generalized instructions from Google on this process can be found here:
https://support.google.com/cloudidentity/topic/9173976?ref_topic=9048334
Go to your Google Admin account at admin.google.com and select 'Apps.' Then, select LDAP from the Apps menu.
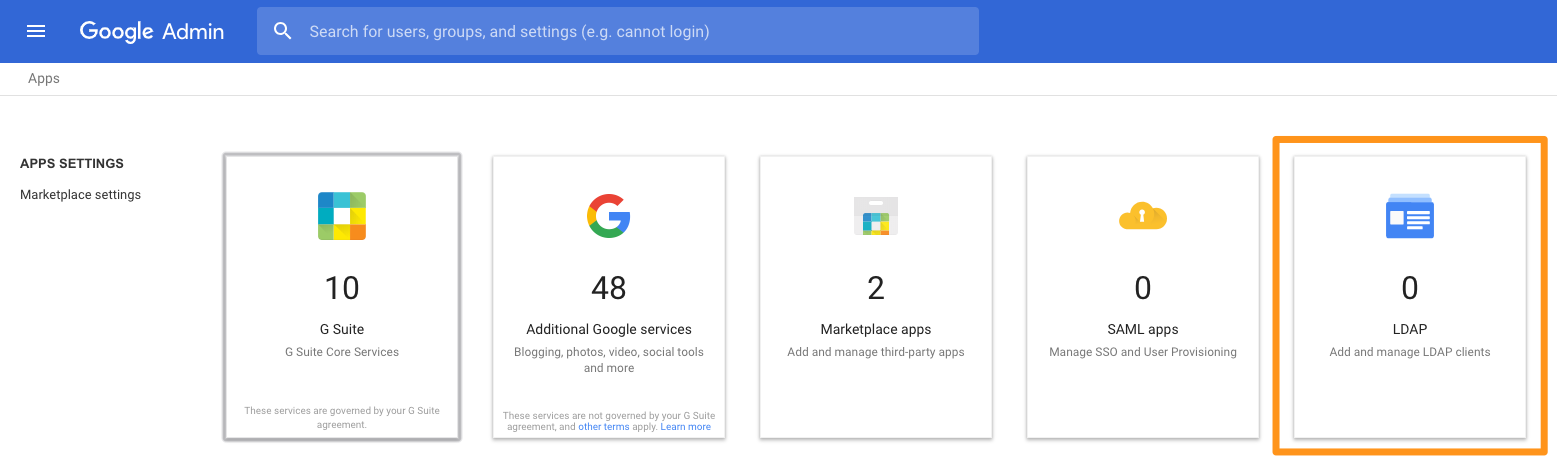
Apps menu
Click 'ADD CLIENT'. Then name the client appropriately.
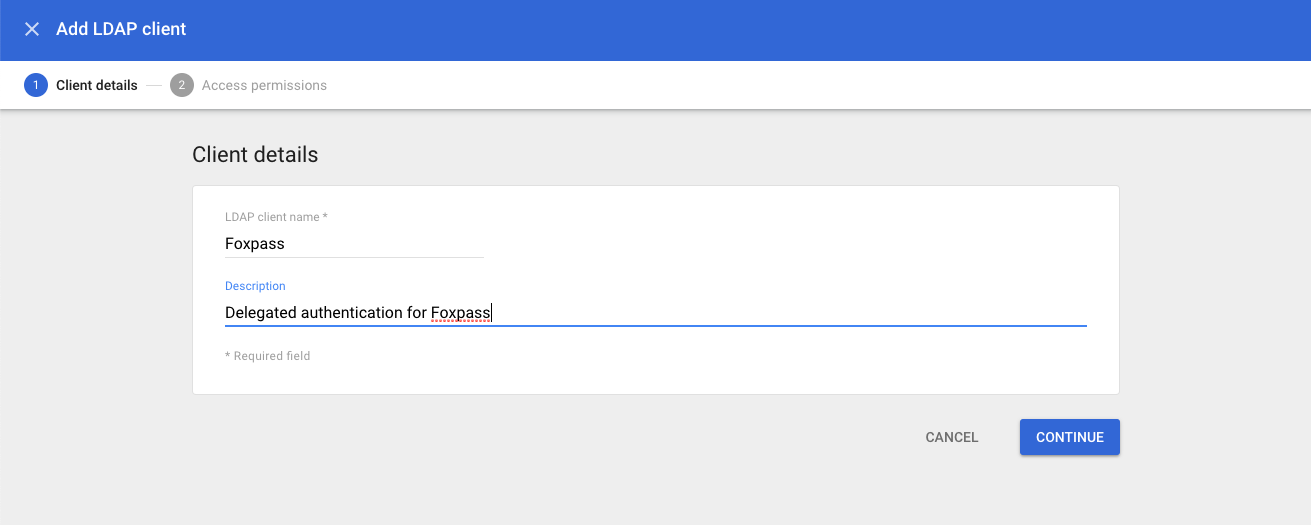
Naming your client
Next, set permissions for the Foxpass connection. For delegated authentication, Foxpass needs credential verification for all users that use Foxpass. Select all users or whatever specific OU's you use in Foxpass. Read user information and read group information permissions are not necessary.
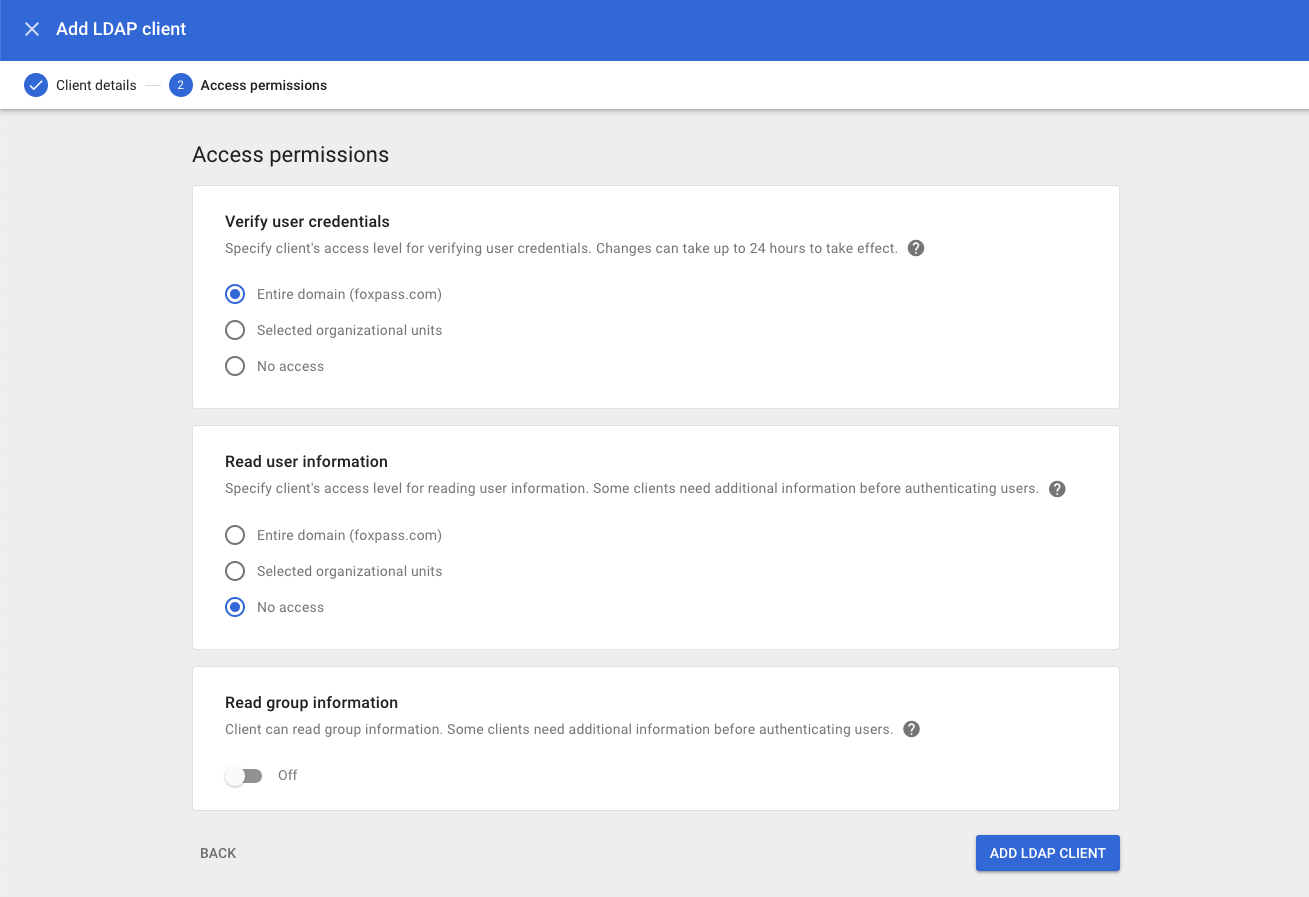
Permissions settings
Then, download and unzip the certificate and key from Google. You should have a .crt and a .key file. You'll upload these into Foxpass later.
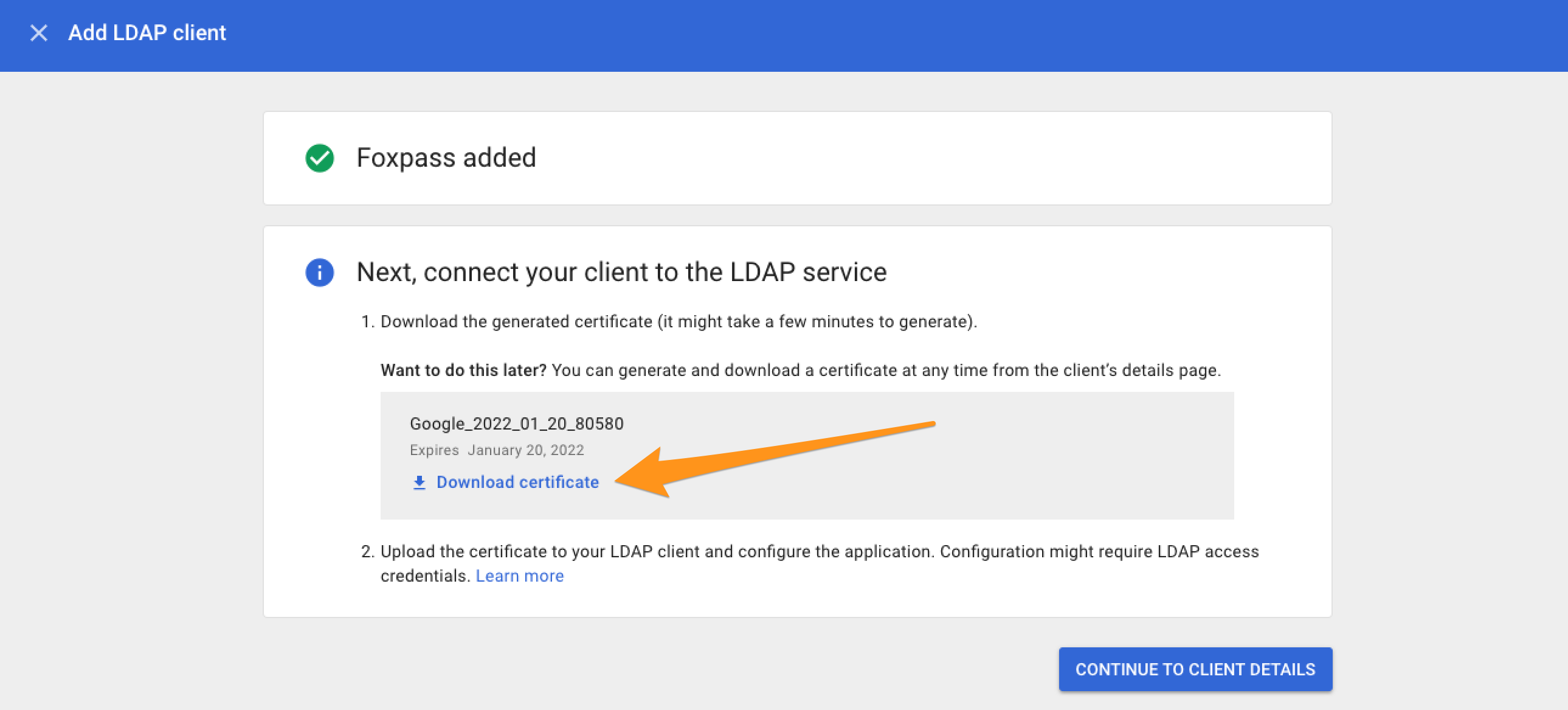
Download certificates
Finally, enable the Foxpass integration by setting the status to ON and saving the settings in the Google console.
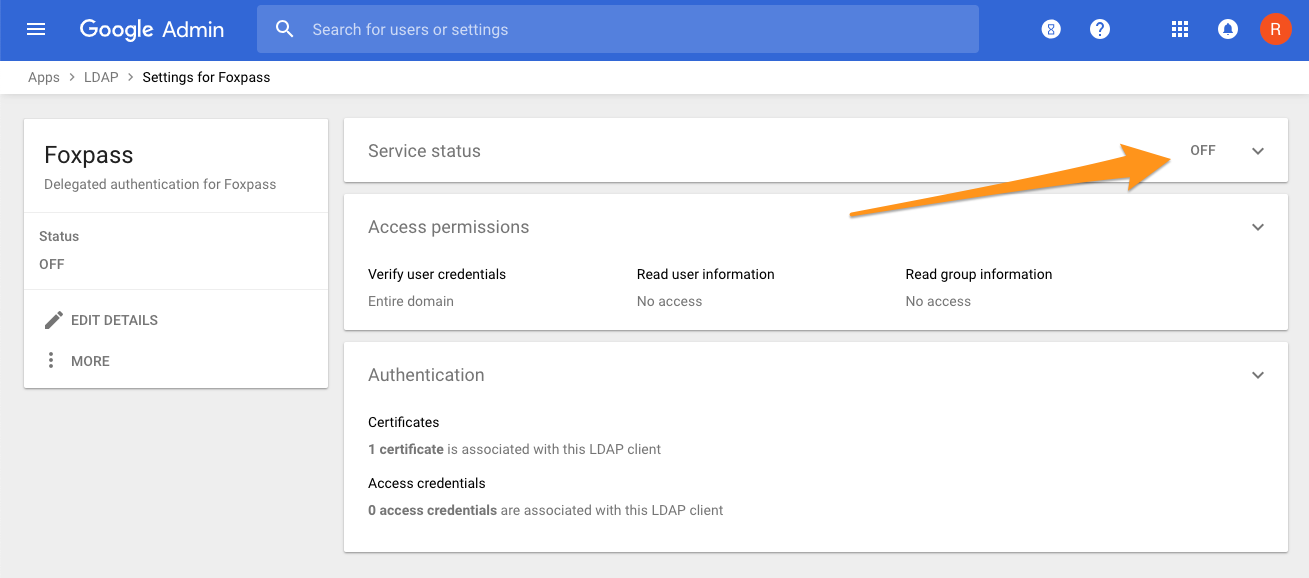
Client details
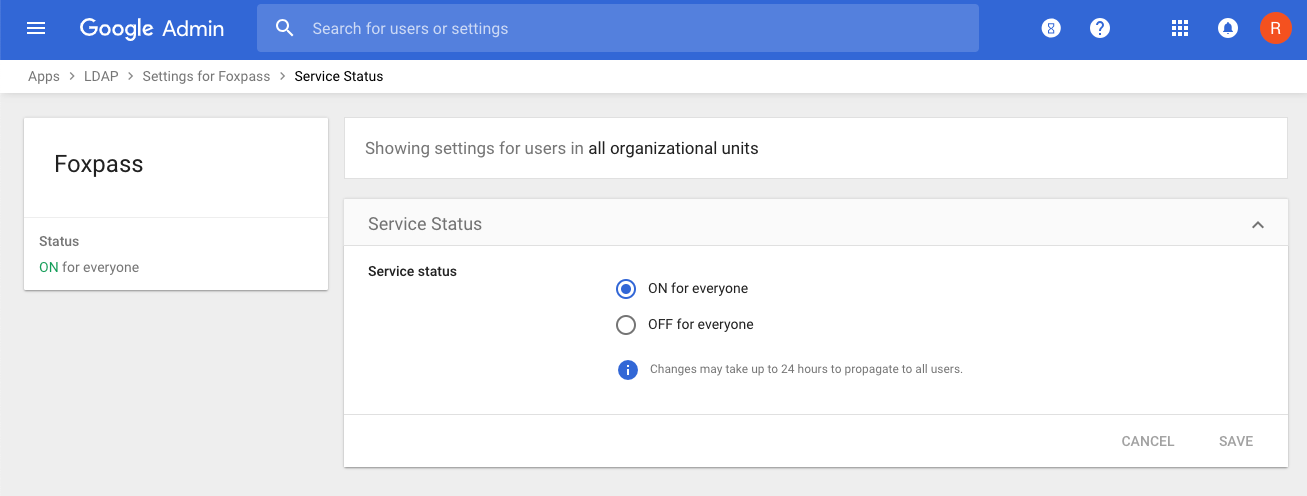
Status page
Set Google Secure LDAP as your Delegated Authentication type
Go to the Foxpass 'Auth Settings' page. Go to the "Password authentication delegation" panel. Choose Google Secure LDAP from the dropdown menu. Next, upload your certificate and key from the previous section and click save.
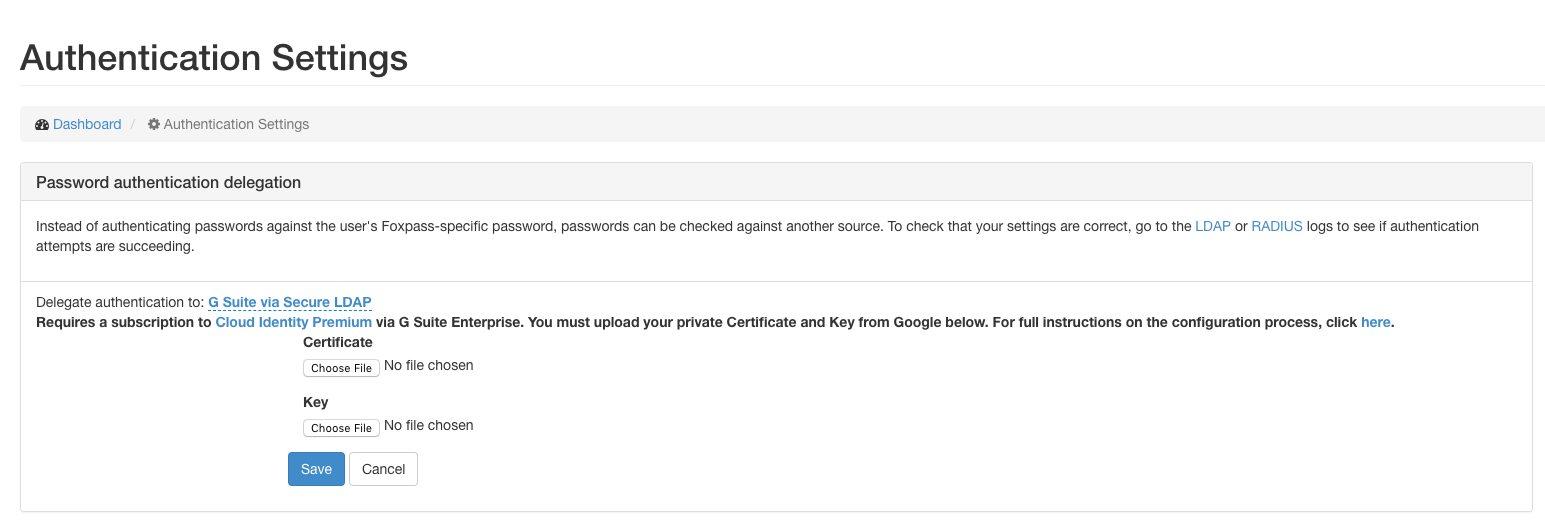
Foxpass Authentication Settings console
Now, try signing into one of your systems that's configured with Foxpass using your Google password and you're all set!
Common Issues & Debugging
If you're having authentication issues, you'll want to check the logs to see what error is occurring under the hood.
You can find instructions on how to check Google's logs here:
https://support.google.com/a/answer/9394001
Foxpass logs for RADIUS and LDAP can be found here:
https://console.foxpass.com/settings/radiuslogs/
https://console.foxpass.com/settings/ldaplogs/
Common error codes:
| Error code | Possible issue |
|---|---|
| INSUFFICIENT_ACCESS | - incorrect user password - user is missing Enterprise or Cloud Identity Premium license - LDAP client is disabled in Google |
| SERVER_DOWN | - incorrect certificate/key combination |
I just made a change in Google and nothing is happening:
Wait 10 or so minutes and try again. Google takes time to update.
What if my issue isn't listed here:
Read Google's guide on common error messages:
https://support.google.com/cloudidentity/answer/9167101?hl=en&ref_topic=9048334
Updated 7 months ago
