Intune-MacOS
Configure EAP-TLS on Foxpass
Please follow the EAP-TLS initial setup guide to create client CA, server CA and SCEP endpoint if not configured already.
Configure Intune for Initial Setup
If you are configuring SCEP certificates for both Windows and macOS, you only need to follow the initial setup documentation once
Please refer the Intune for Initial Setup documentation to configure the Intune initially.
Upload Apple MDM Push Certificate
-
In the Endpoint manager, now go to devices → macOS enrollment.
-
Click on Apple MDM Push Certificate.
-
A dialog box will open at the right side to configure MDM Push certificate.
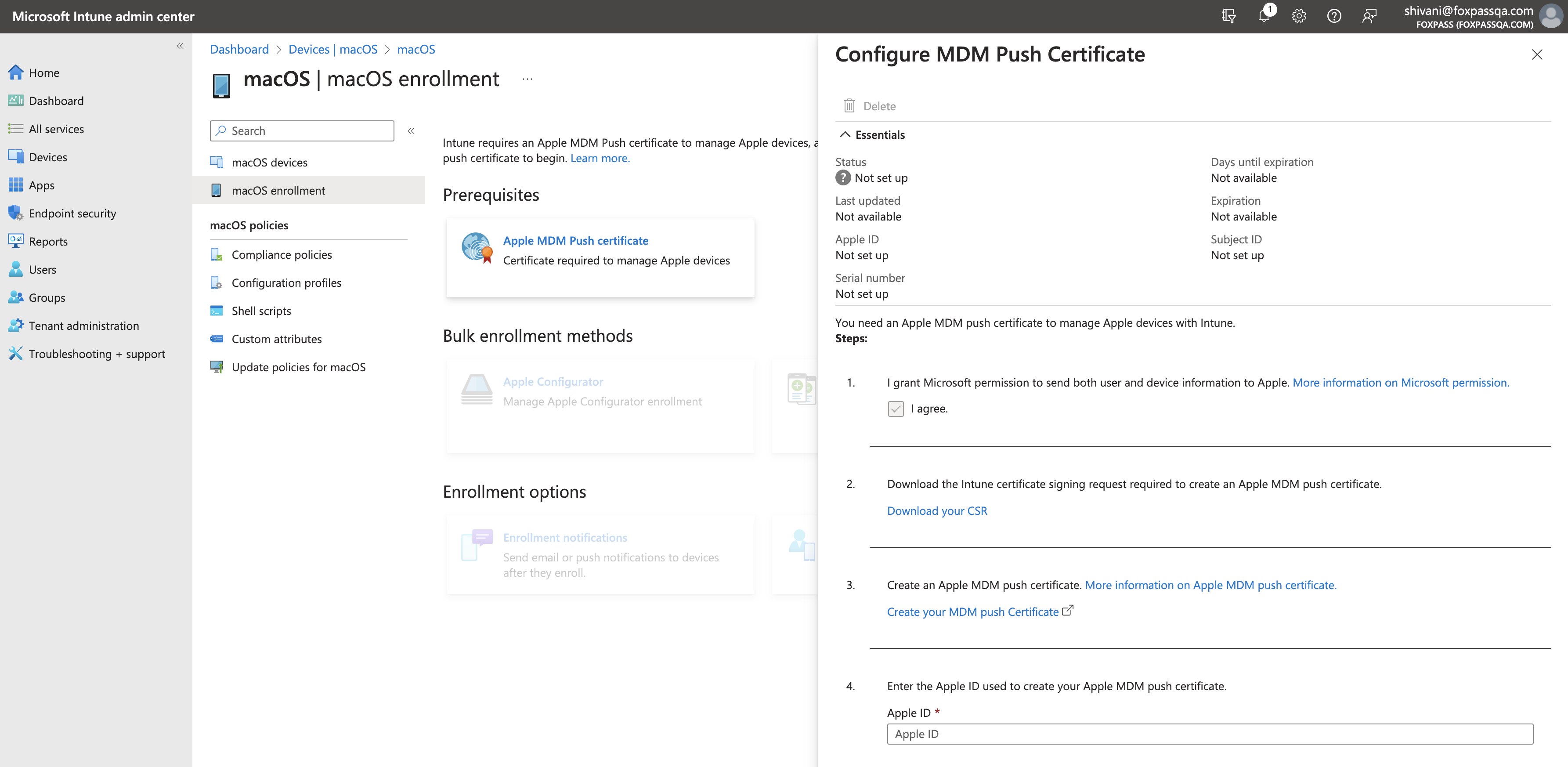
Configure MDM Push Certificate
-
Click on Download your CSR link.
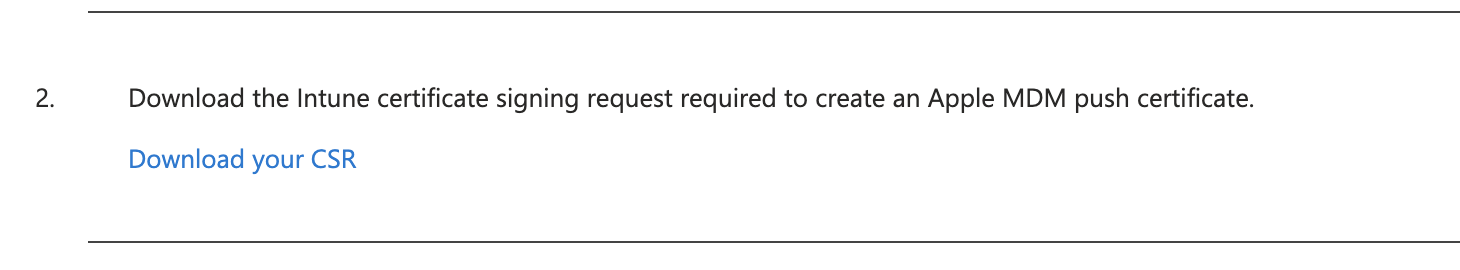
Download your CSR
-
Click on Create your MDM push certificate./
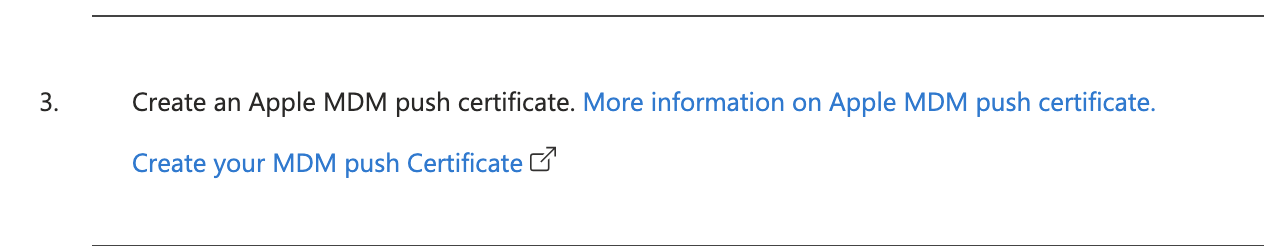
Create your MDM push certificate
-
Sign in to your Apple account and click Create a certificate button.
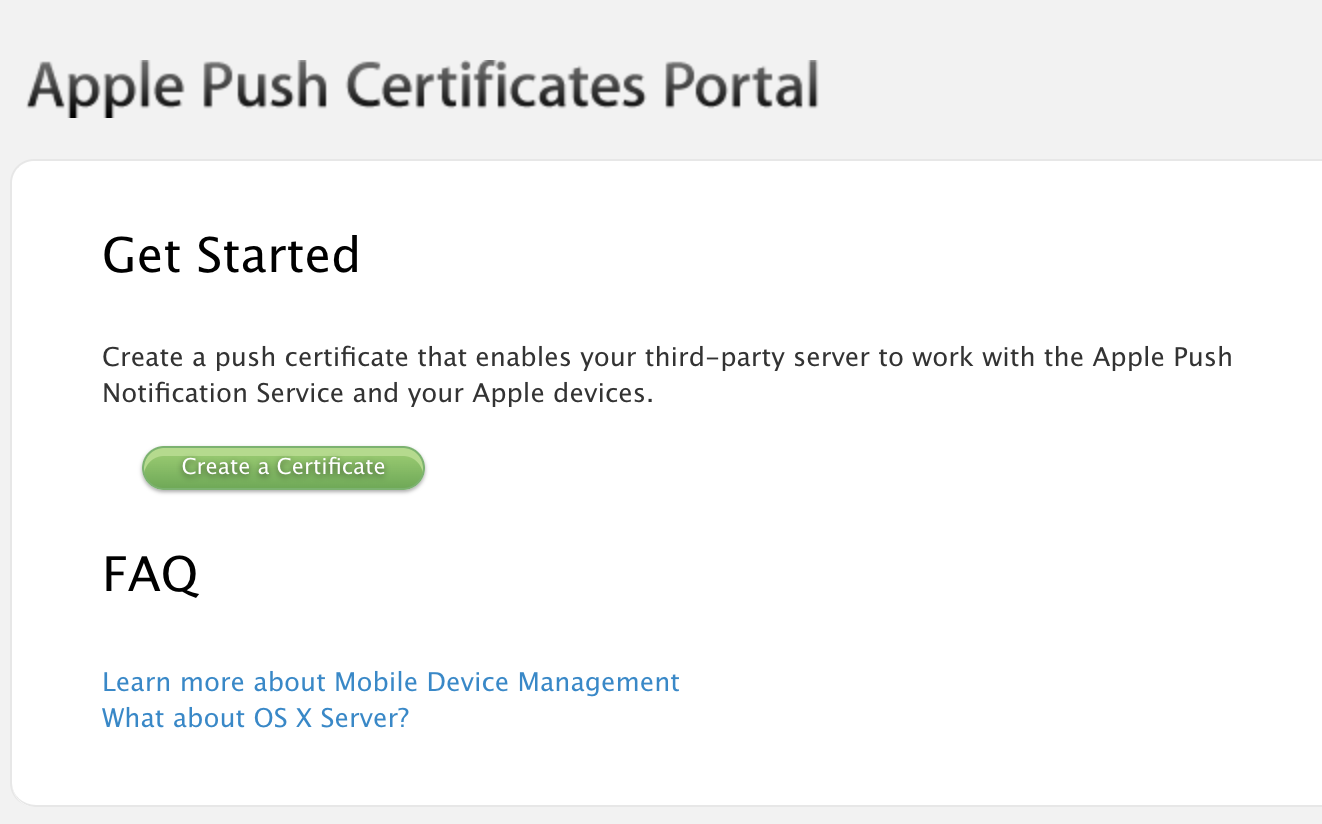
Create a certificate
-
Upload previously downloaded CSR.
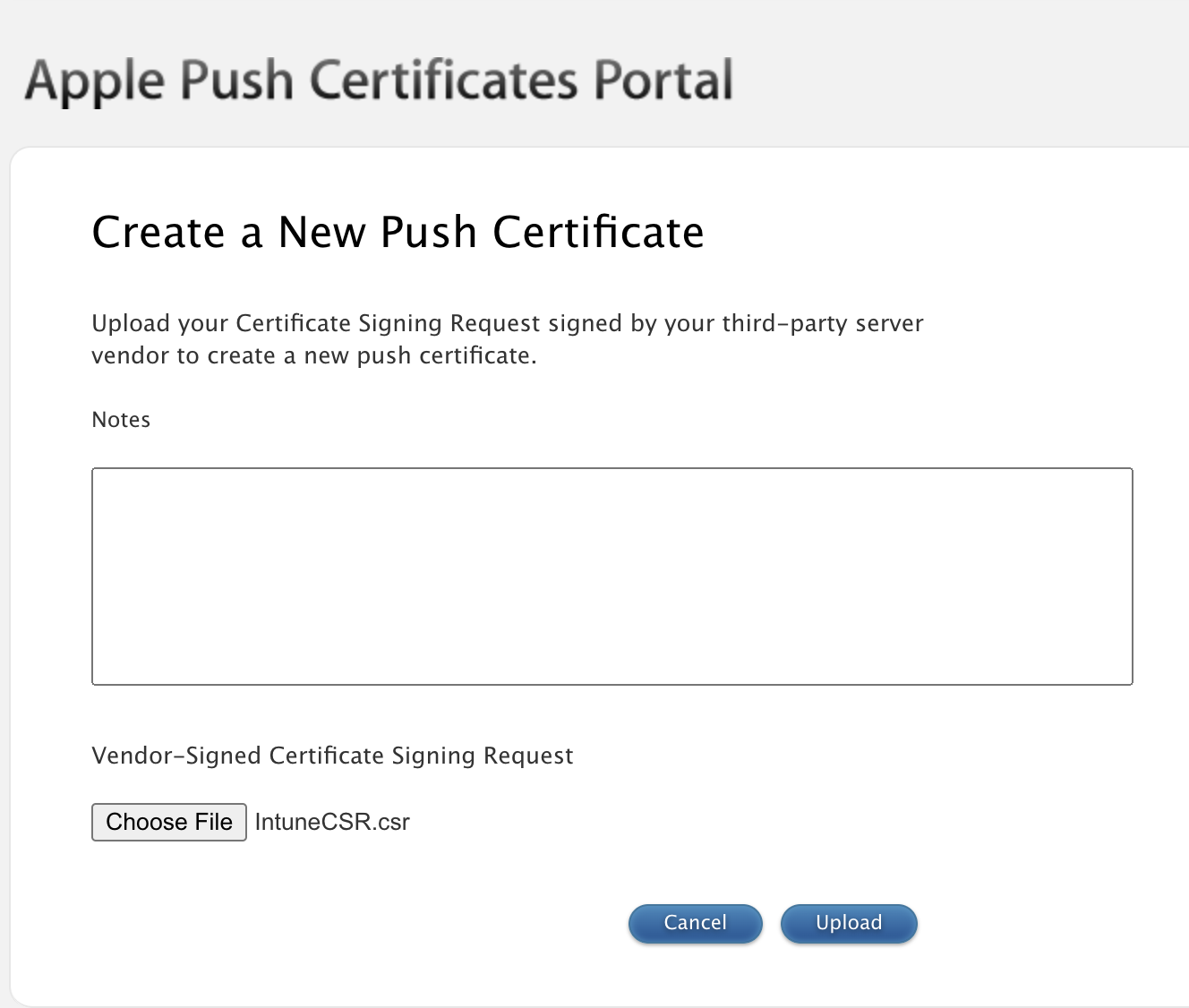
Upload CSR
-
You will see a confirmation message of certificate created. Click on 'Download' button.
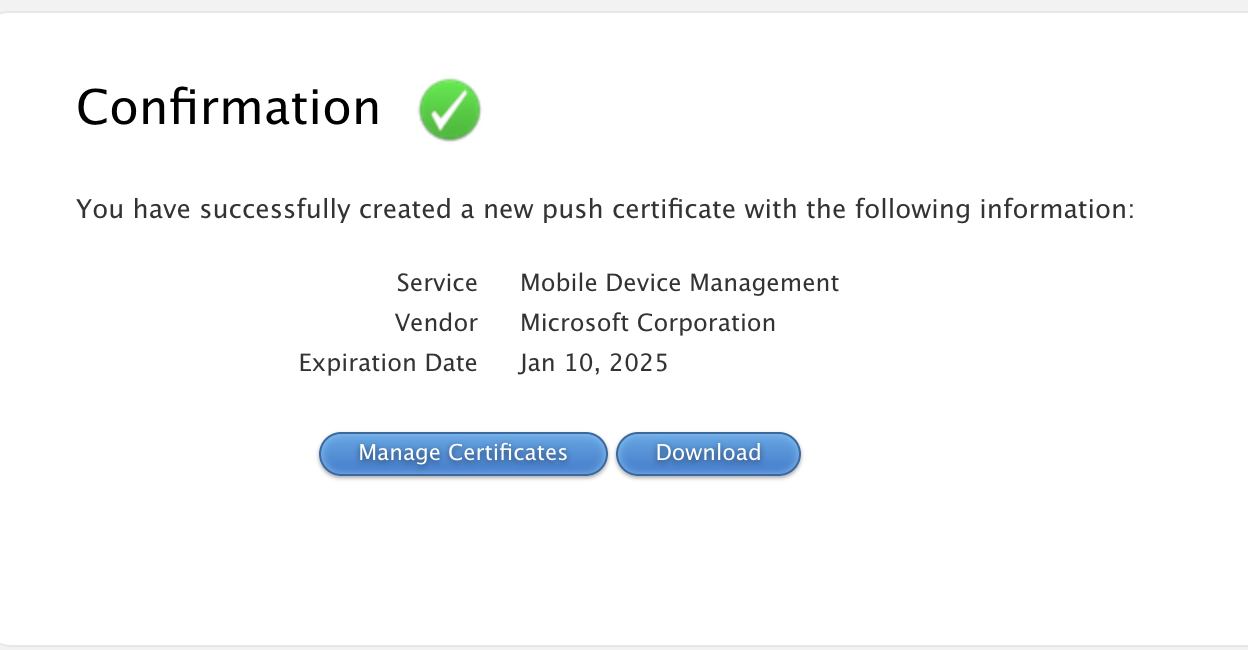
Download certificate
-
Upload the downloaded certificate in Intune.
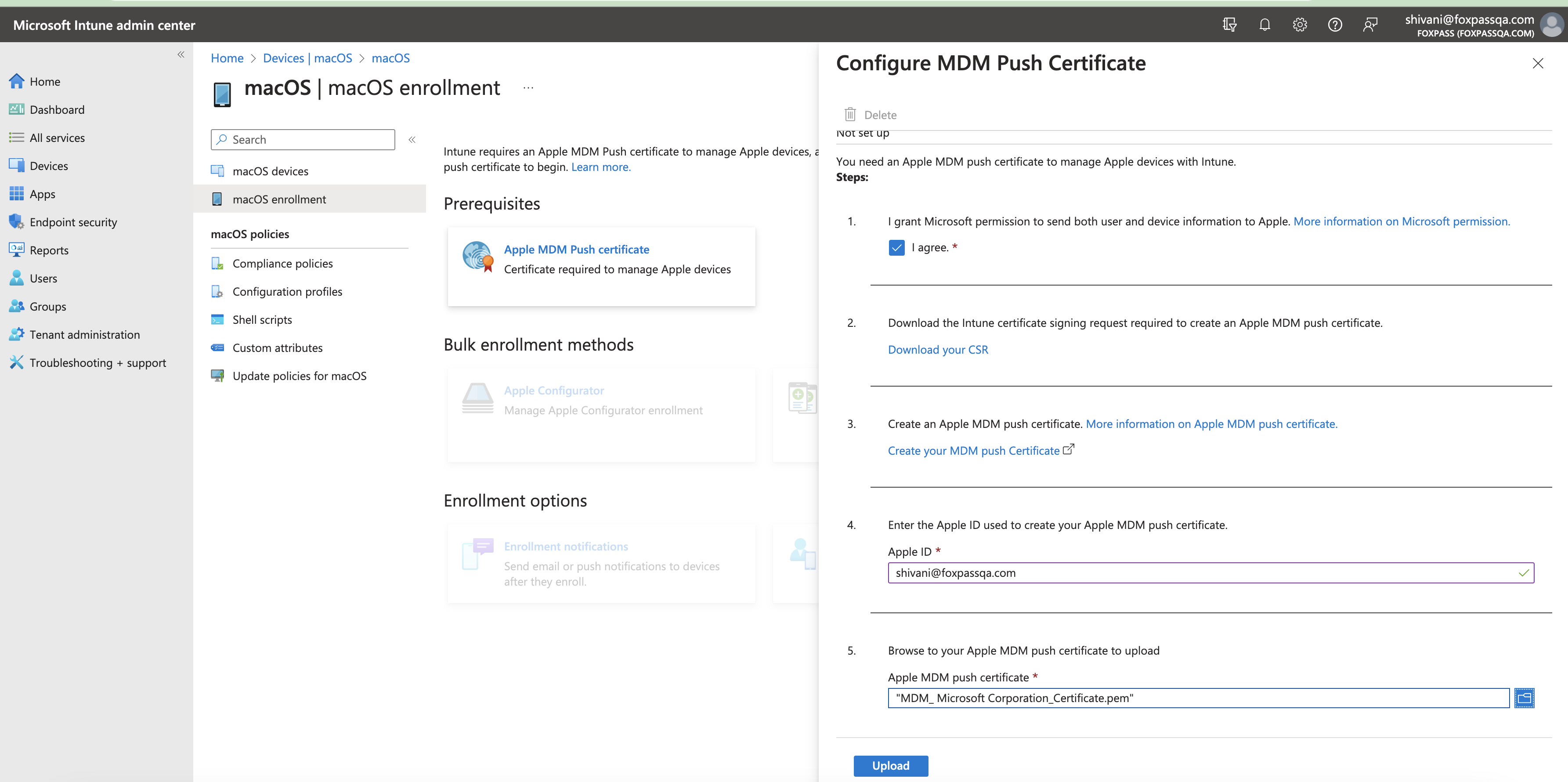
Upload push certificate
Create Configuration Profiles
- Go to the configuration profiles of macOS. Click on Create > New Policy.
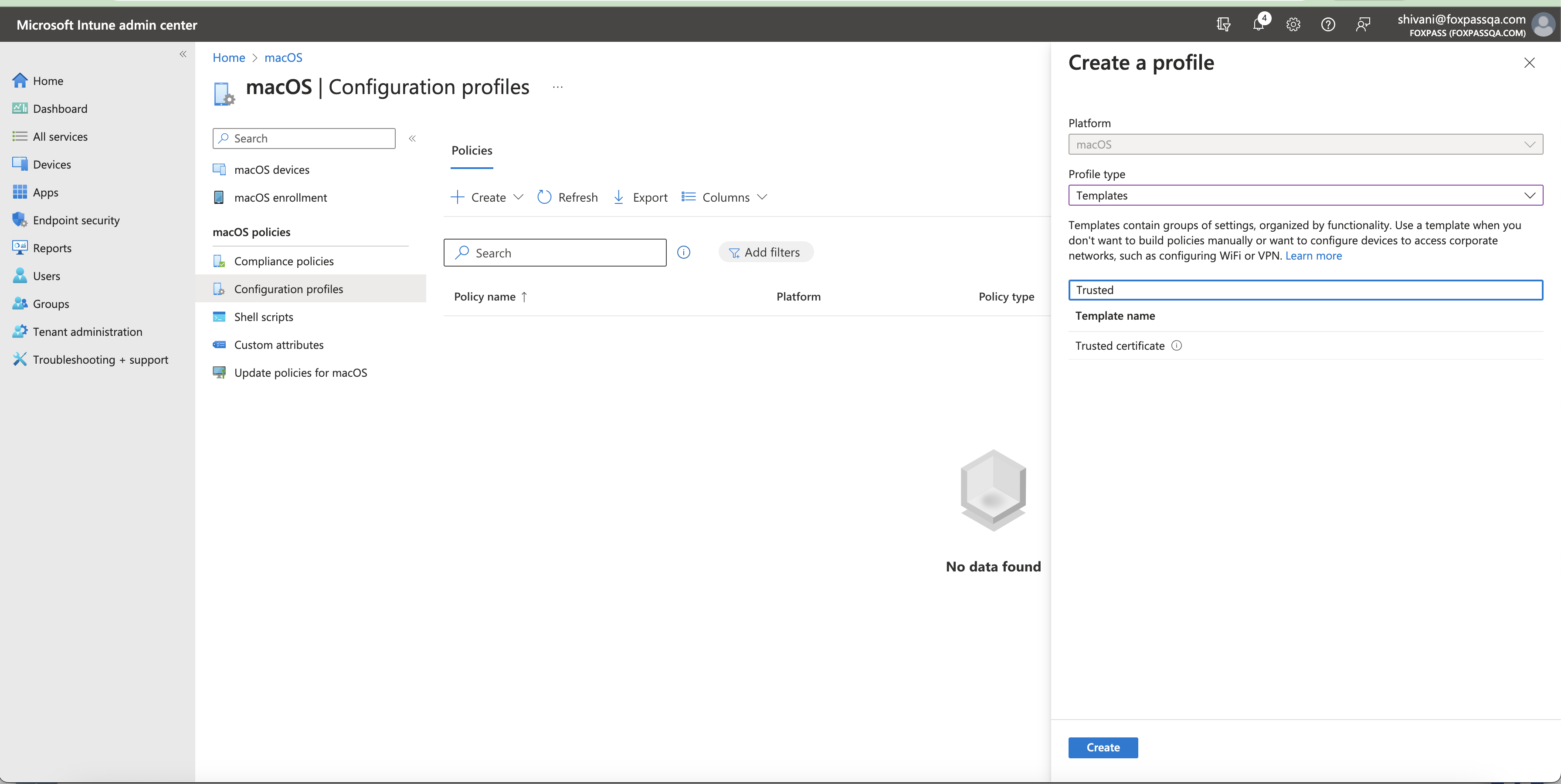
Click 'Create'
Create a Client CA Profile
- Create a new Client CA profile for macOS using the Trusted certificate template. Upload the Foxpass Client CA cert in the client profile.
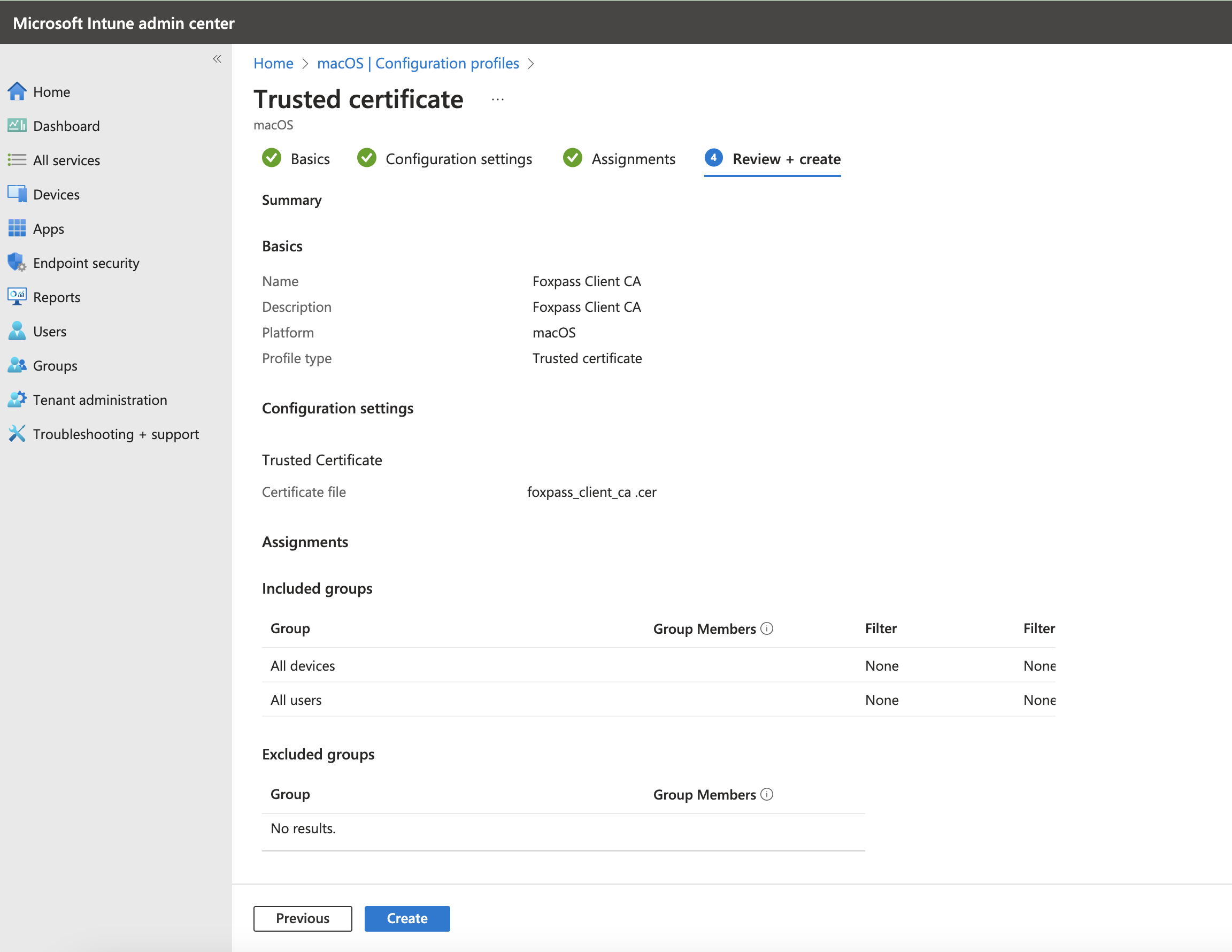
Review and Click Create profile
Create a Server CA profile
- Create a new profile for macOS using the Trusted certificate template. Upload the Foxpass Server CA cert in the server profile.
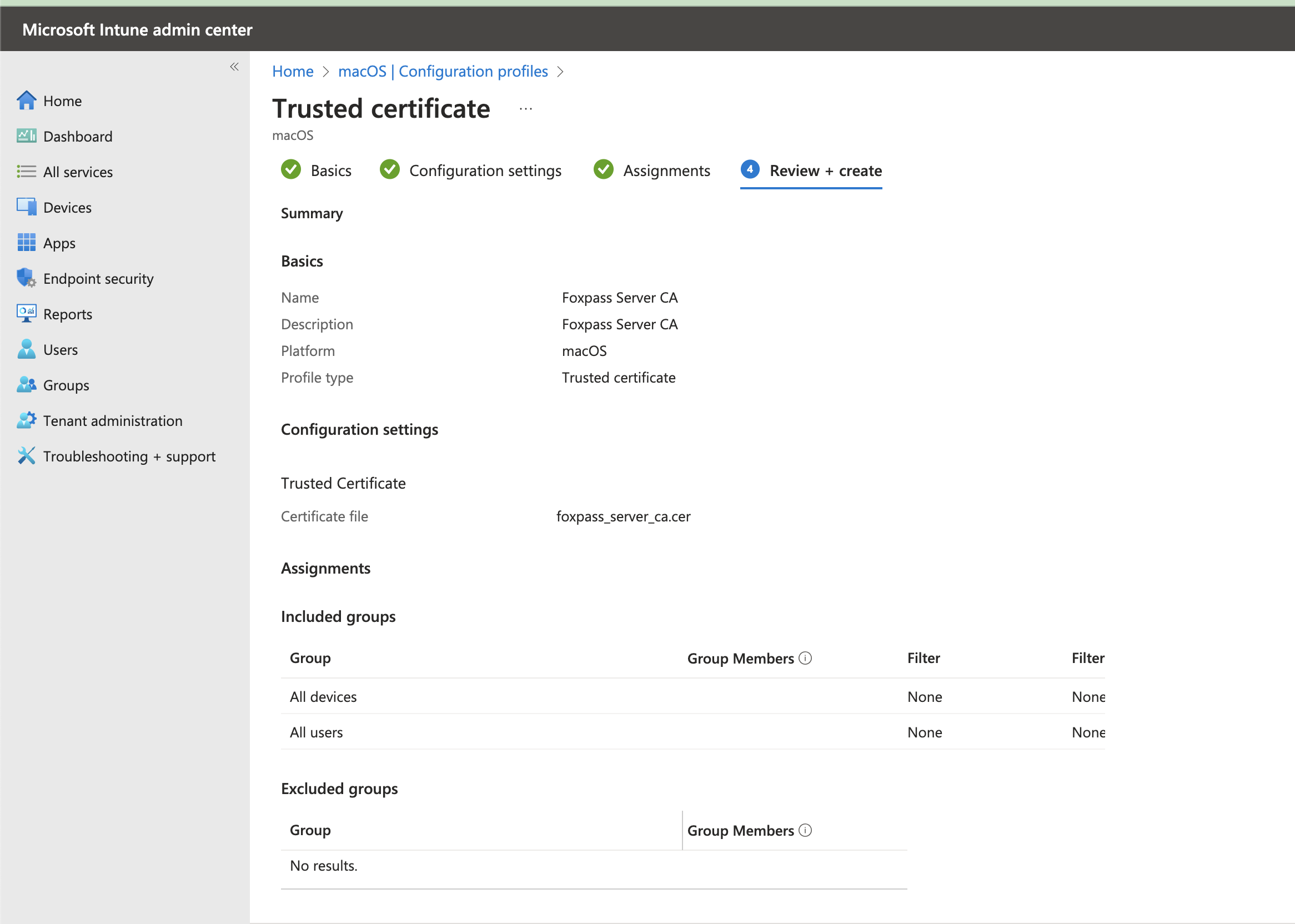
Foxpass Server CA Profile
Create a SCEP profile
- Make sure the SCEP endpoint is configured correctly in Foxpass.
- Create another new profile for macOS using the SCEP certificate template with these settings:
You need to make sure that every user has an EmailAddress set in their Azure User Profile. If not, SCEP the profiles will not install.
-
Name: Foxpass SCEP
-
Certificate type: User
-
Subject name format: CN={{UserName}},E={{EmailAddress}}
-
Subject alternative name: Add 1 attribute:
- Email address as {{EmailAddress}}
- URI as IntuneDeviceId://{{AAD_Device_ID}} (This is required if you want to check device compliance during EAP-TLS request)
-
Certificate Validity period: Years: 1
-
Key usage: Digital Signature
-
Key size: 4096
-
Hash algorithm: SHA2
-
Root certificate: Select cert from Foxpass Client CA from first item in this section
-
Extended key usage: Add both
- Any Purpose (2.5.29.37.0)* (optional)
- Client Authentication (1.3.6.1.5.5.7.3.2)*
-
Renewal threshold (%): 10
-
SCEP server URL: Foxpass SCEP endpoint from the SCEP page
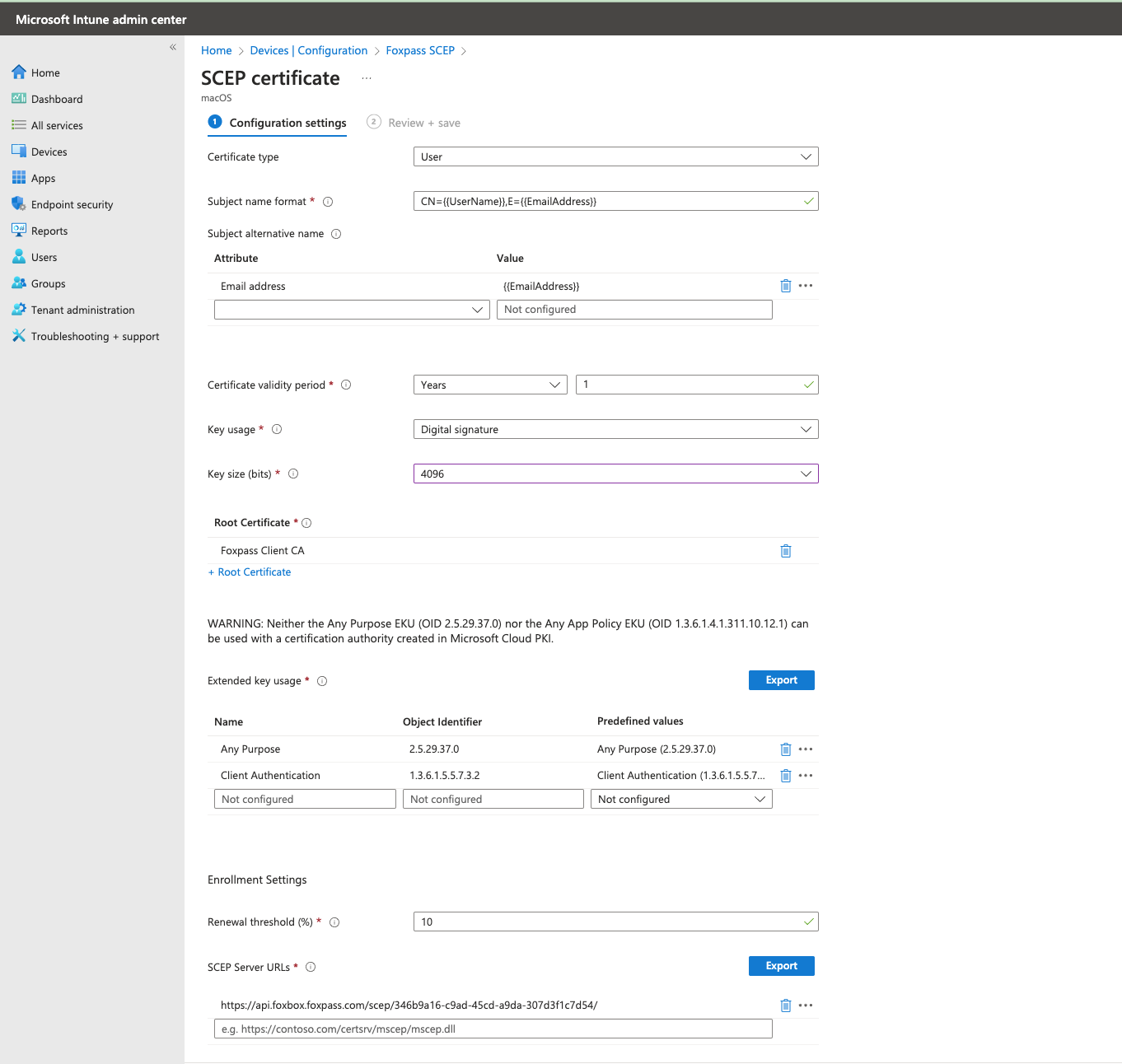
Sample SCEP Profile
Create a Wi-Fi Profile
- Go to Configuration Profiles of macOS devices > Create New Policy > Profile Type > Templates > Choose WiFi as the template name.
- Name: Foxpass Wi-Fi
- Wi-Fi Type - Enterprise
- SSID -
<Your SSID> - Connect automatically: (your choice)
- Hidden network: Disable
- Security Type: WPA/WPA2 Enterprise
- Proxy settings: None
- EAP-Type: EAP-TLS
- Root certificates for server validation: (Choose Foxpass Server CA uploaded previously in this step)
- Client Authentication - Certificates: Foxpass SCEP
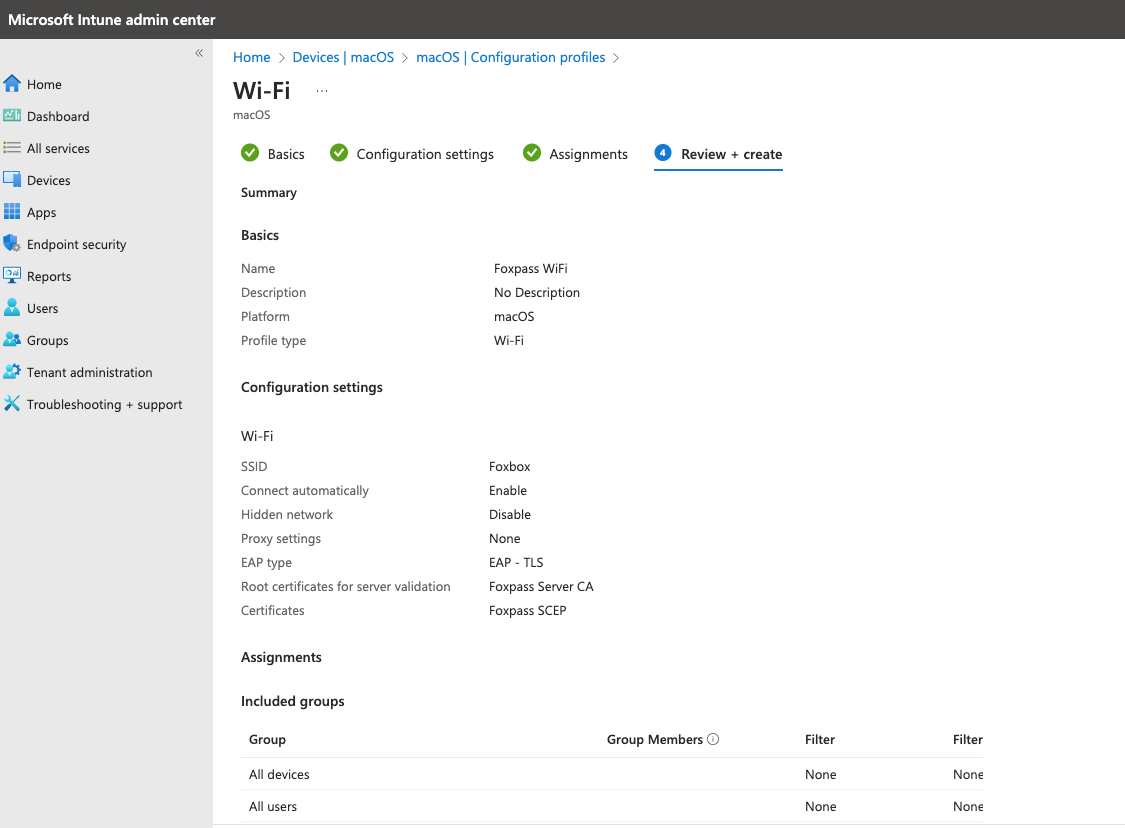
Review Wi-Fi profile
Now, setup your Macbook
- Go to portal.manage.microsoft.com, download and install intune company portal.
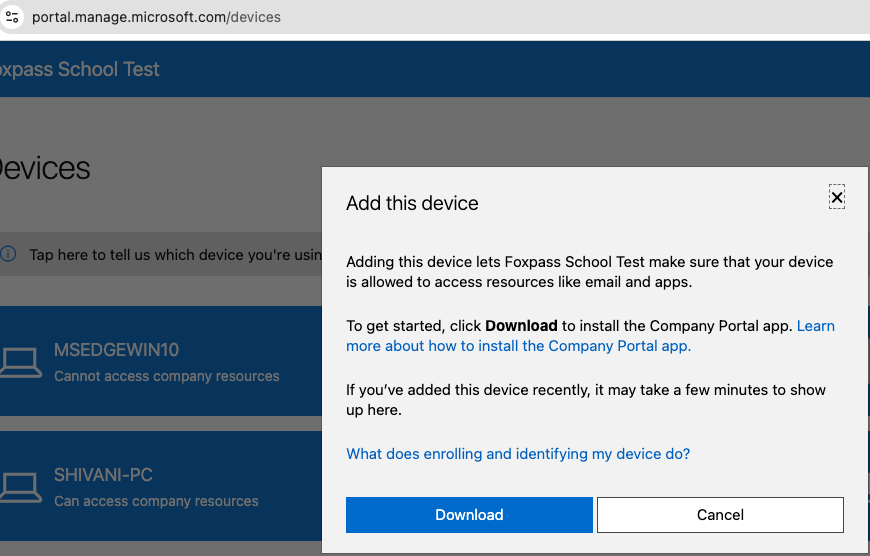
Download company portal
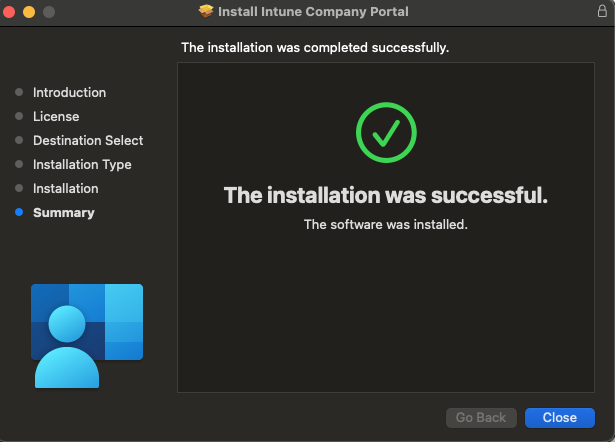
Install Company Portal
- Open the Company Portal app and sign in. Click 'Begin' > Continue.
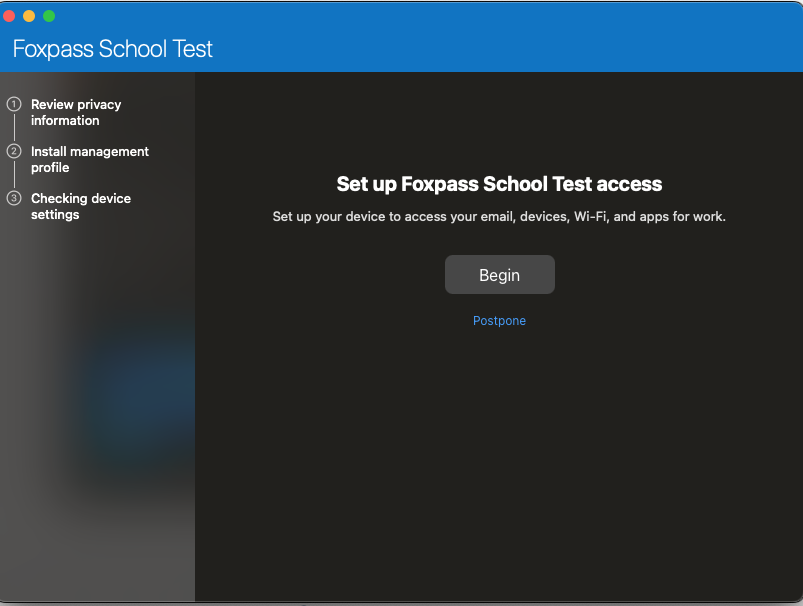
Click Begin
- Click on the Download Profile.
- Go to System settings > Profile > Management Profile
- Install the management profile.
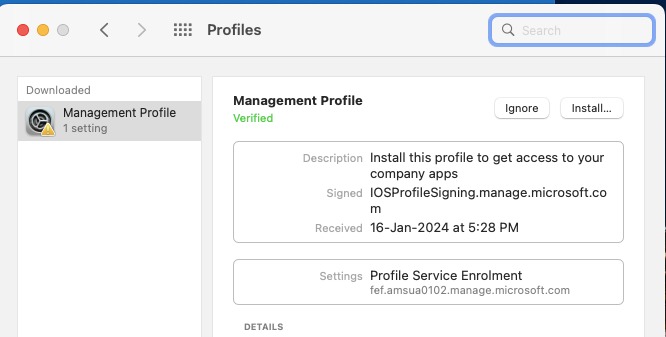
Install the management profile
If all goes well, you will now be able to see your device enrolled in Intune and the Foxpass Console's EAP-TLS.
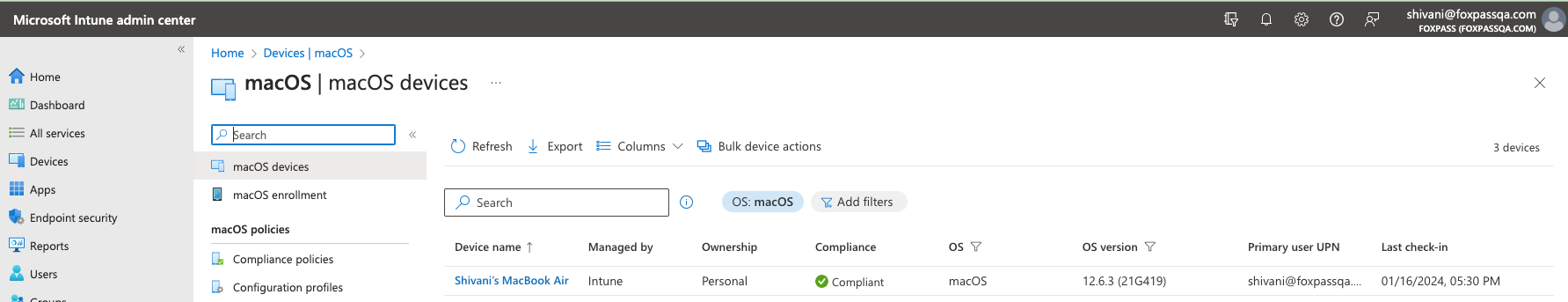
macoS device enrolled in Intune
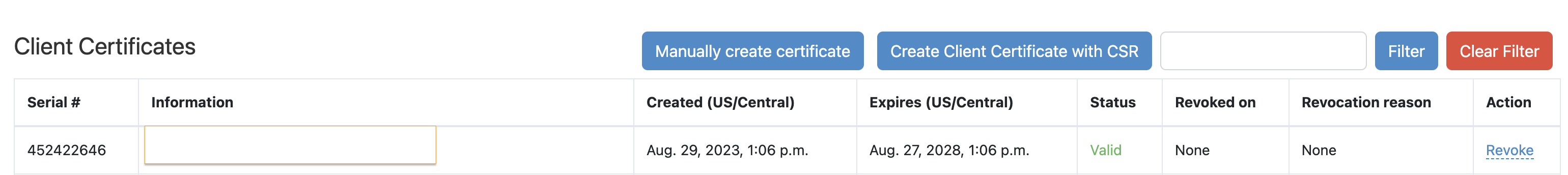
Client Certificate - Foxpass
You can see Foxpass Client CA, Server CA and Client Certificate in Keychain Access on your Macbook.
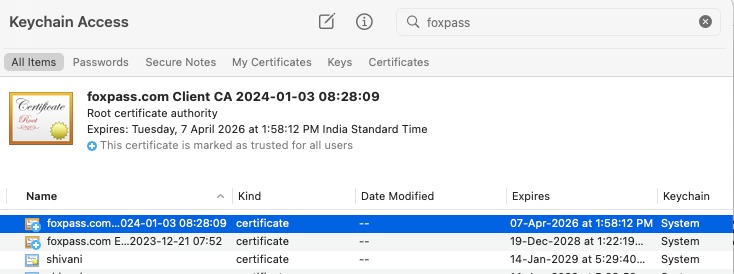
Certificate and CA's in Keychain Access
You can also see successful/unsuccessful logs on the RADIUS logs page.
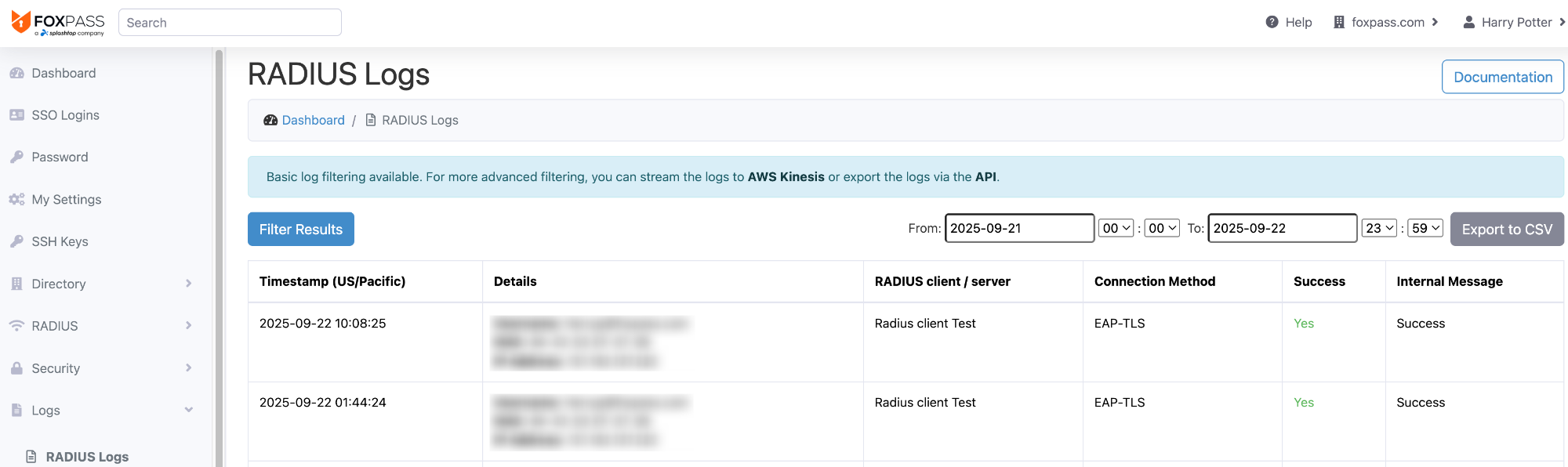
RADIUS logs page
Still having problems?
Updated 6 months ago
